Net Threats: Knowing the dos and don'ts of posting on social media
Apr 22, 2011
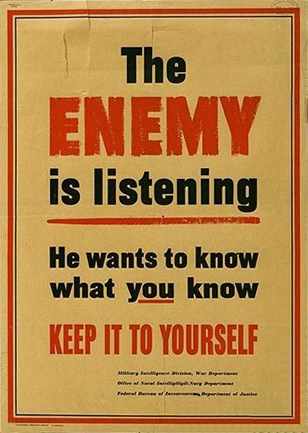
BAMBERG, Germany, April 22, 2011 -- During World War II, the U.S. government adopted the slogan "loose lips might sink ships" to warn people to be careful when talking in public. Started in 1942 by the U.S. Office of War Information, the "loose lips" slogan was coined to help the public understand that casual conversations about sensitive information could tip off enemies.
Almost 70 years later, the same slogan could be used in relation to today's tweets, posts and published photos in the online world of social media. With the proliferation of social media sites such as Facebook, Twitter, YouTube and Flickr, the world has turned into a global network of connections and open source information.
Seemingly, innocent comments or posts could be used by terrorists and media organizations to negatively affect the military. Whether you are a Soldier, spouse or relative, community members need to be aware that what they post, however innocent, can have ramifications.
THE DANGER
Social media sites are great, especially for military families. They allow Soldiers and their families, who may move many times throughout a career, to stay connected with friends and family worldwide by allowing us to share our thoughts, photos and events throughout deployments. Even people's daily life and military experience is shared for all the world to see. But that doesn't mean that anything goes.
"Social media provides the opportunity for Soldiers to speak freely about what they're up to or what their interests are," according to the U.S. Army Social Media Handbook. "However, Soldiers are subject to (Uniform Code of Military Justice) even when off duty, so talking negatively about supervisors, or releasing sensitive information is punishable under the UCMJ."
Spouses and family members, while not subject to UCMJ, also need to be careful what they post.
"Sharing what seems to be even trivial information online can be dangerous to loved ones and the fellow Soldiers in the unit - and may even get them killed," the handbook said. "America's enemies scour blogs, forums, chat rooms and personal websites to piece together information that can be used to harm the United States and its Soldiers."
Many people think that if it's unclassified information, it's safe to post, said Tonya Heinbaugh, U.S. Army Garrison Bamberg security officer. However, it's those small pieces of information that could be the most harmful.
"I don't think spouses and sometimes, even Soldiers, realize how great a threat it is," Heinbaugh said. "They only need bits and pieces of information."
In fact, it's unclassified information that can be the most harmful. According to the "Manchester Papers," an Al-Qaeda terrorist training manual found in England in 2000, more than 80 percent of all the information the terrorist group received was through unclassified material, Heinbaugh said.
That was even before social media sites took off, she said. So that number has probably dramatically increased.
"Think what they are collecting now," she said. "We give them all the information they need."
Those small bits of information can be added to other items you have already posted or will post in the future. For example, you generalize and say that your husband has deployed to Afghanistan. While looking through your photos on Facebook, someone might be able to see the unit patch on your husband's Army Combat Uniform or notice you are a "fan" of a specific unit's Family Readiness Group.
Those little pieces of information can be put together to give the enemy a larger picture.
"Even small pieces of information can do harm when they pair it with other information," Heinbaugh said.
For instance, when a group of 173rd Airborne Brigade Combat Team was redeploying back to Bamberg this fall, one careless post from a spouse on Facebook naming the time of the return, caused the entire flight to be delayed due to operational security concerns, said Heinbaugh.
"Our adversaries are trolling social networks, blogs and forums, trying to find sensitive information they can use about our military goals and objectives," wrote former Sgt. Maj. of the Army Kenneth O. Preston in the social media handbook. "Therefore, it is imperative that all Soldiers and family members understand the importance of practicing good operations security measures."
According to "Killing with Keyboards," an operational security training slideshow, anyone can be a target.
However, some community members may think that enemies wouldn't read their profile or comments because they aren't anyone special or important.
"That may be true for now, but you never know when one online posting will bring you to their attention," the training states.
Others might say that they don't have any enemies.
The information can be used by not just terrorists but by former girlfriends, boyfriends of divorced spouses, the report states. Angry neighbors, disgruntled co-workers and even identity thieves could use the information you posted.
How to avoid revealing too much
If information on social media sites is being used by the enemy, is the answer to stay off the internet highway? Realistically, the answer is no. Social media sites are here to stay and are becoming an even more important tool in communication in modern technology. However, you can take some precautions to help keep both you and your loved ones safe.
"The adversary -- Al Qaeda and domestic terrorists and criminals for instance - have made it clear they are looking. When using social media, avoid mentioning rank, unit locations, deployment dates, names, or equipment specifications and capabilities," the social media handbook said.
Don't talk about unit morale, said Heinbaugh, who said that things such as bad equipment or not enough equipment, bad leadership and other complaints can be used by the enemy.
And, in fact, it's not just social media sites. Commenting on newspaper articles, blogs or other public forums can also give away more information than you intend.
For example, Heinbaugh said that a recent article about a local commander in the "Stars and Stripes" caused many people within the unit to comment on the newspaper's website. These comments exposed a low morale and even possibly leadership problems within the unit. All this information can be used by the enemy.
"If they know you are upset, they could target you," she said. "If a person is upset, they may vent or get emotional and could reveal more things than they should."
Take a close look at all privacy settings, especially on Facebook. Heinbaugh recommends checking out your setting at least once a month. Often, the website administrators will change or add security features without letting the customers know. She also recommends changing your privacy settings to be "friends only."
Talk to members of your extended family and friends about what they can post. How well do you know your "friends" on Facebook? If you have several hundred "friends" chances are you don't know all of them that well. In addition, it's easy to fake an account, Heinbaugh said.
"What you post to friends is not the same thing you would post to someone who is just an acquaintance," Heinbaugh said.
Do not reveal sensitive information about yourself such as schedules and event locations, the social media handbook states. Ask, "What could the wrong person do with this information?" and "Could it compromise my safety or that of my family or my unit?"
Look at photos, as well as what you post. Geotagging is a feature that reveals your location to other people within your network, the social media handbook states. Consider turning off the GPS function of your smart phone. In the same way, videos can be damaging as well. Make sure the videos don't give away sensitive information.
If damaging information has already been posted, that's not an excuse to post sensitive information. Some spouses, Heinbaugh said, have the attitude that since Soldiers post things that it's fine for spouses to post information.
"That's not an excuse to keep doing it," she said. "Two wrongs don't make a right. You can't control anyone but yourself."
If you see information posted you think is inappropriate, contact the site administrator, she said. The administrator can delete the comment and send the person a personal message explaining the reason for the deletion. If you reply in the comment section that the information is a violation of operation security that just waves a red flag to others about the information. The more you are aware, the better protected you are, Heinbaugh said.
"These are not personal forums," Heinbaugh said. "They are public forums. In a technology world, not much is private anymore."
To read more about the U.S. Army's social media regulations, log onto http://www.slideshare.net/USArmySocialMedia/armysocial-media-handbook-2011or to read "Killing with Keyboards" log on to www.slideshare.net/pastinson/killing-withkeyboards.
Article from Army.mil = link = http://www.army.mil/-news/2011/04/22/55381-net-threats-knowing-the-dos-and-donts-of-posting-on-social-media/index.html?ref=home-headline-title6